The following is an outline of a presentation to the Computer Club of the Sandhills (June 12, 2017) at the Whispering Pines Town Hall. It includes examples, links to free software, articles, and informative websites.
Based on my experience this guide contains the most important tips for setting up a VPN service for a typical home I have called this presentation "Using a VPN (Virtual Private Network) for the Home" because it takes advantage of the free VPN solutions available for Chrome, FireFox, and Opera. Also I will briefly discuss some more comprehensive (and more expensive) VPN implementations including using a dedicated VPN router and paid VPN service. I hope this information will help save you time and frustration, and perhaps some money!
Interesting article on VPNs I just came across: 7 Reasons Why VPNs Might Die Out by 2020. (The article assumes you understand the basics of VPN implementation.)
|
-
0. Why all this talk about VPNs now?
- VPNs have been around for a long time (20 years or so). Until recently they have been used almost exclusively to connect mobile employees with their company network, or to connect different branches of a company with each other and the home office. Some self-employed workers have used their own VPNs to connect from their mobile location back to their office. But the advent of VPNs for the average user is undergoing a spectacular growth. The prinicipal reasons for this are embodied in two concerns: privacy and security. Privacy and security are overlapping concerns and some people tend to confuse these. First, what do we mean by Internet Privacy? "Privacy can entail either Personally Identifying Information (PII) or non-PII information such as a site visitor's behavior on a website. PII refers to any information that can be used to identify an individual."
Here are The Five Biggest Threats to Your Privacy in 2017.
Some expert observers believe that the era of the anonymous use of the Internet is past - The reasons you can't be anonymous anymore.
The recently enacted bill in Congress now allows your ISP to collect information from your Internet activity (mostly browsing history) and sell this to any and all without your permission. This will principally used for directed advertising, but could conceivably be used for other purposes.
- Here are the details about the effect of this legislation:
What does the new ISP data-sharing rollback actually change?
- What has this to do with Internet Security?
Internet security involves two aspects: protecting your devices from threats (viruses, trojans, worms, i.e., malware of many kinds) and protecting your PII (personally identifiable information) from being captured (such as credit card, bank, social security info) that could be used to commit fraud.
- Using a VPN may protect privacy to a certain extent, but a VPN will not protect against malware threats. Why?
Malware threats generally originate in the user's behavior (carelessness).
For example:
- Failure to keep the computer OS updated. This is especially important for Windows, witness the recent highly publicized WannaCry Ransomware exploit. Windows 10 turned out to be immune to this exploit because it forces updates!
- Failure to employ a good anti-virus and keep it updated (antivirus routers, like the new Norton Core Router or TP-Link's Mesh Router, are beginning to be available that update themselves without user intervention).
- Careless behavior such as opening email links/attachments without due consideration (or perhaps at all, even "from friends") - not much to done here except get everyone educated. Here is a recent article on the Email Threat Vector. Here is a nice infographic on this issue.
- Finally there is the ubiquitous Web Page Threat Vector, where simply visiting an infected page is enough to infect your computer. This can be mitigated greatly by using a anti-virus that checks web pages for infection before you visit them, as for example the free Avast Online Security Chrome extension. Many paid antivirus products supply this functionality (e.g., Norton and AVG). Opera has this protection built-in. None of these is going to be absolutely 100% effective, just as no anti-virus is absolutely 100% effective.
- Your PII will almost certainly be protected by SSL connections (see https:// or the little lock or secure indicator at the beginning of the address). So for these purposes (unless you are in the habit of sending someone your credit card, bank, social security info in an email) you need not worry. BUT, if your computer has been compromised and a keylogger has been installed, the jig is up.
1. What is a VPN and how does it work?
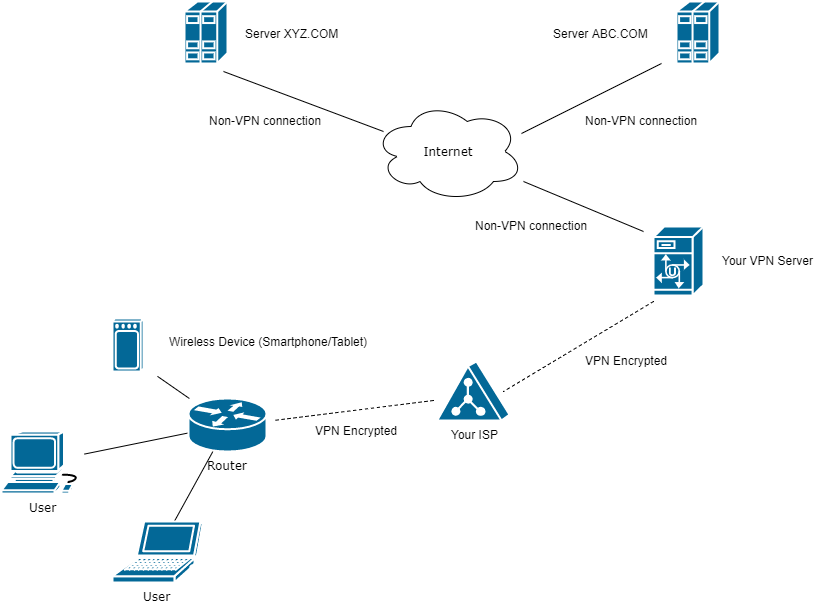
- Basic VPN mechanics from a home user's point of view. See the diagram to the right:
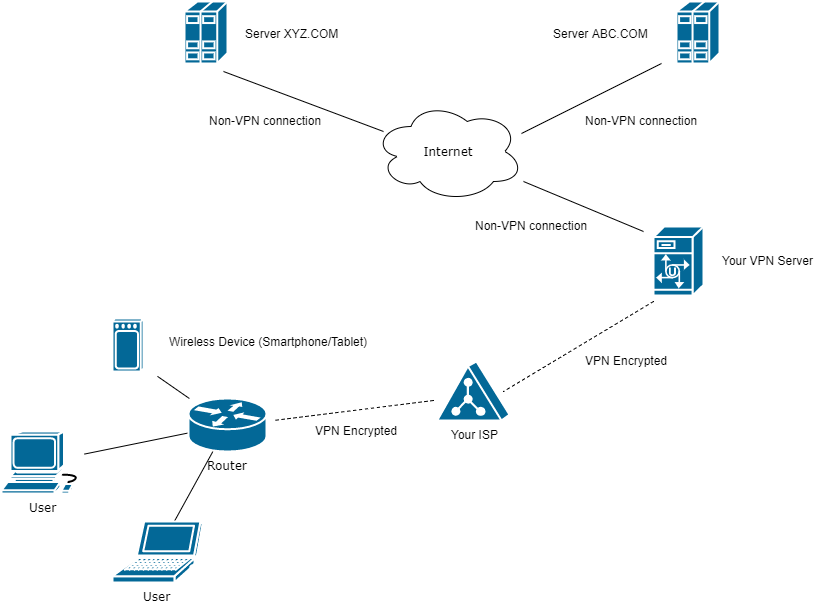
- Normally your Internet browsing traffic (and email, etc) flows through your ISP's gateway unencrypted (except for https:// traffic mentioned above).
This means that the ISP can gather all you activity (sites you visit, searches you make) into a log and sell this information (with PII removed) to interested customers (generally advertisers).
- With a VPN connection in place your traffic will be encrypted before it leaves your computer and will pass through your ISP gateway and be decrypted at your VPN services' server and that traffic, now unencrypted, passed on to destination servers on the Internet. Return traffic from those servers is encrypted before being sent back to your computer. If the ISP captures your traffic it will be useless to them or anyone else because it is all encrypted. The destination servers will see the IP address of the VPN, not your IP address.
Here is an illustration:
- Your IP address and location is visible to any server you visit: IP and location is where we are now
- Now with a VPN service in place: IP and location is somewhere else
- A somewhat technical explanation of how VPNs in general work.
- Another explanation here: a beginner's guide to VPNs.
- All VPNs will slow your Internet connectivity - how much of a slow down you will experience is highly variable. You can count on at least 10% slowdown even with the fastest paid service. If you have a very fast Internet connection this may not matter so much. But, you may find your web browser slowing to a crawl, especially with some of the free VPN services. Some VPNs may not work at all with streaming services, or are so slow as to make them unusable.
2. When would you want/need a VPN?
-
- If you use a public WiFi hotspot such as Panera Bread or McDonald's with a smartphone or laptop, a VPN would be good idea. Why? Because all traffic on an open WiFi connection can be captured with a packet analyzer. If the WiFi connection is secured with WPA2 security protocol it is safely encrypted on its journey between your device and the router. At the router the traffic will be decrypted before being sent on to your ISP gateway.
- If on principle you want to retain as much digital privacy as possible. BUT, ...
- In which case you might consider giving up Google, Facebook, Amazon, PayPal, EBay, Twitter, etc, etc. Here is a Google Privacy Policy Notification I received while doing a search this morning. See how one person chose to deal with Google's data gathering: How I deleted Google from my life. Social media are arguably more a leak (or flood!) of personal data than anything else.
- See 8 Instances You Weren’t Using a VPN, but Should’ve Been. This article has a lot of good info on particular technical features of VPN services as well.
3. How would you implement a VPN at home?
- VPNs usage for home (non-business) use can be implemented three ways:
1. By using a browser extension.
For instance, here are VPN extensions available for Chrome and FireFox. Opera has a VPN built-in.
(I have found Hotspot Shield works well for Chrome. Also available for Android and IPhone, and as a desktop client for Windows and Mac, but only as a free trial that requires entering credit card info.)
2. By using a desktop client.
You would want to employ a desktop client to protect non-browser Internet clients, such as email programs like Windows Live Mail, as well as all browsers running on the computer at the same time. There a few free desktop client VPN services available but are generally either so slow, are only trial versions, or cap your bandwidth to such low levels they are not worth employing. This provides an encrypted connection for all Internet clients. A notable exception may be an IOS app (thus usable on IPads and IPhones) called FreeVPN. I have tested it and it works remarkably well. OperaVPN is a free app for IOS and Android.
3. Get a VPN enabled router and purchase a VPN service.
Although the most expensive and most difficult to implement it has the advantage of protecting all router connected devices, including desktops, laptops, tablets, phones, video streaming devices (Roku, Amazon Fire, Chromecast, Apple TV, etc.).
- Customized Routers from FlashRouters
- I am sure that this year and henceforth many new routers will have VPN client capability built-in allowing you to just sign up for your VPN service and configure the router (as you can do with the FlashRouters above) easily.
- The Fastest VPN [Services] of 2017
|